This is such a serious security flaw that the FTC punished Fandango and Credit Karma for doing the same thing in 2014.
A31a: Burp and Genymotion on Mac or Linux
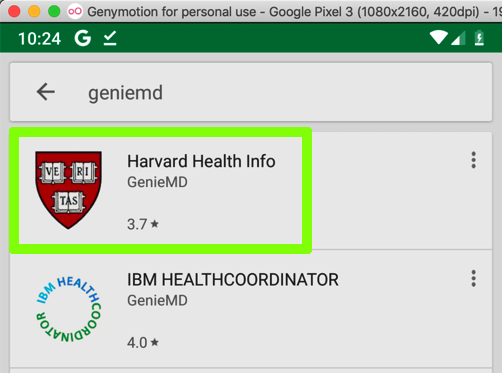
Install the "Harvard Health Info" app, as shown below.
Troubleshooting
If Google Play won't connect, you are probably using the proxy.In Settings, tap Wi-Fi, and adjust the networking to use a proxy of None.
Archived App
If the app is unavailable, use this archived copy.

On your Android device, click SAVE.
At the bottom center of the device, click the round Home button.
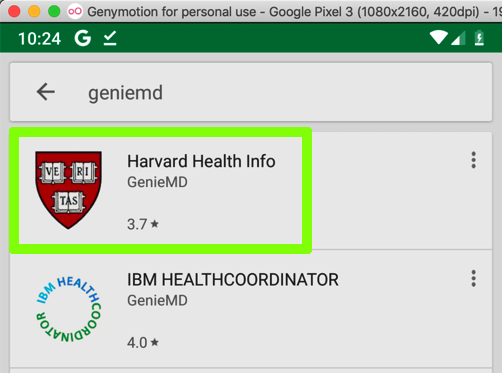
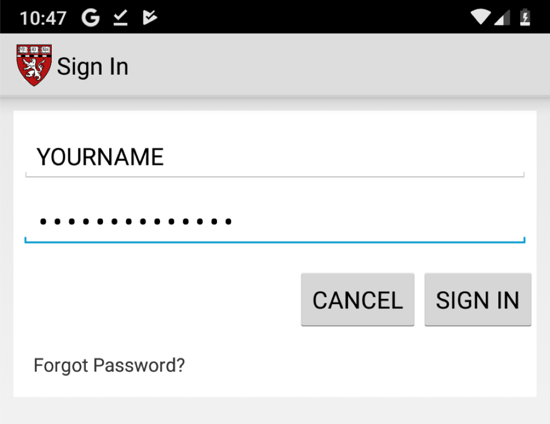
Click "Sign in" and enter test credentials, as shown below.
Click "SIGN IN".
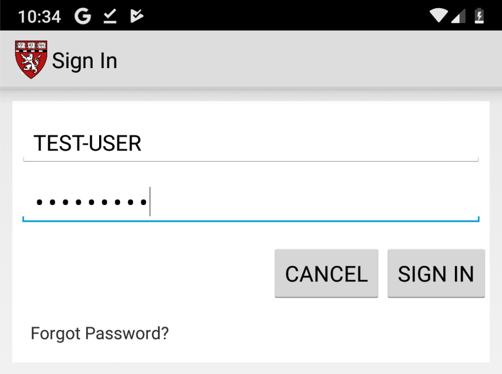
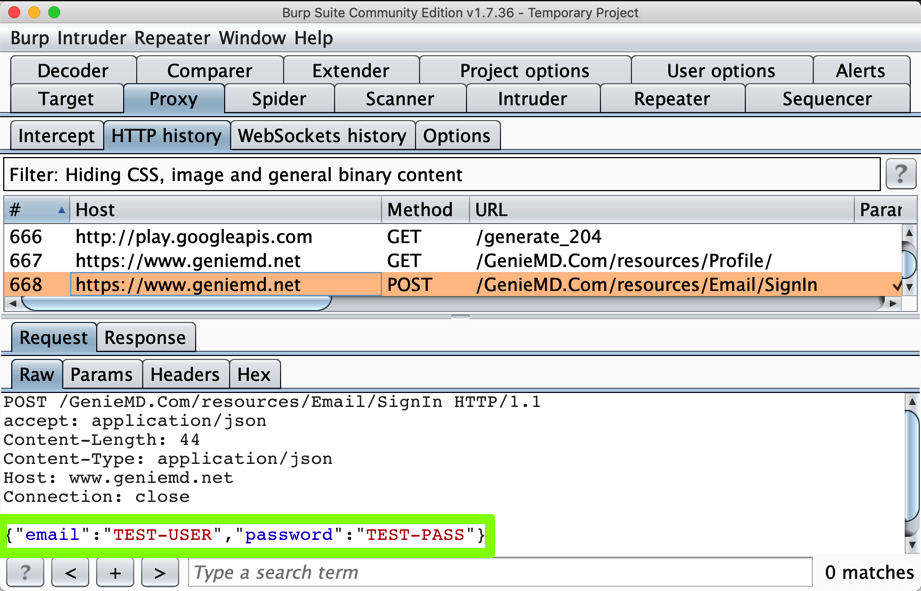
In Burp, on the Proxy tab, click the "HTTP Requests" sub-tab.
Find the POST method going to /GenieMD.Com/resources/Email/SignIn.
The username and password appear in Burp, as shown below:
If you have been doing these projects in order, and you are using a Mac, this is not a security problem, because you have the PortSwigger certificate installed--your Android device has been told to trust Burp.
In Burp, on the Proxy tab, on the "HTTP history" sub-tab, right-click any entry and click "Clear history". Click Yes.
If you are using a Mac or Linux host, do this:
On your Android device, in Settings, click "Security & location", Advanced, "Encryption & credentials", "Clear credentials".
Click OK.
Enter your PIN.
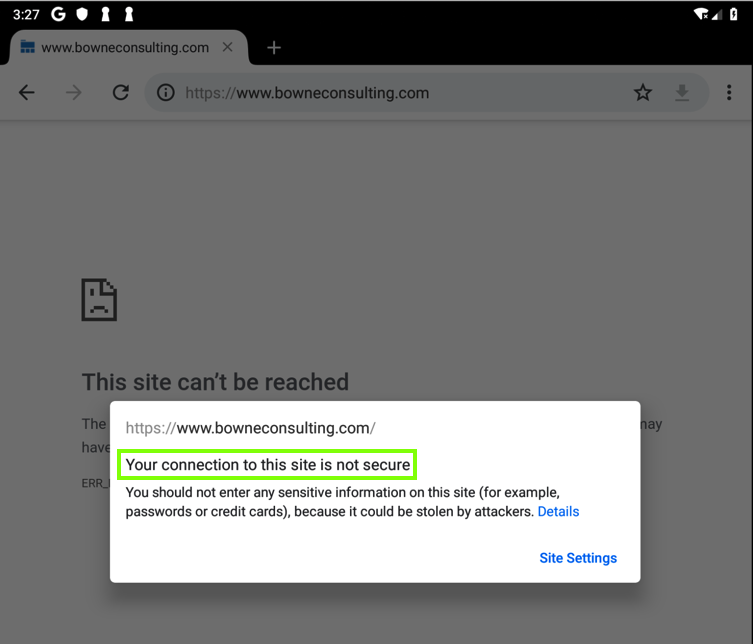
You should see an error message, as shown below.
(When I did this on an Android 9.0 Genymotion device, the green padlock remained visible, even though the page would not load; another Android bug.)
No valid HTTPS connections can be made from your device now, because it no longer trusts Burp.
Click "Sign in" and enter test credentials, including your name, as shown below.
Find the POST method going to /GenieMD.Com/resources/Email/SignIn.
The username and password still appear in Burp, as shown below:
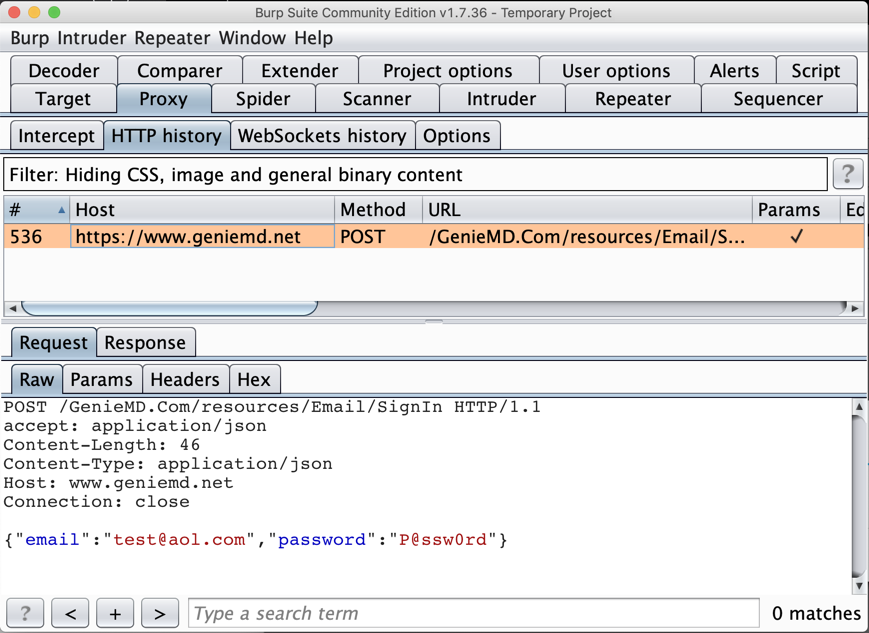
This is a big problem--the MITM attack is allowed. GenieMD exposes its users to this attack, because they don't bother to validate SSL certificates.
The flag is the text covered by a green box in the image below.
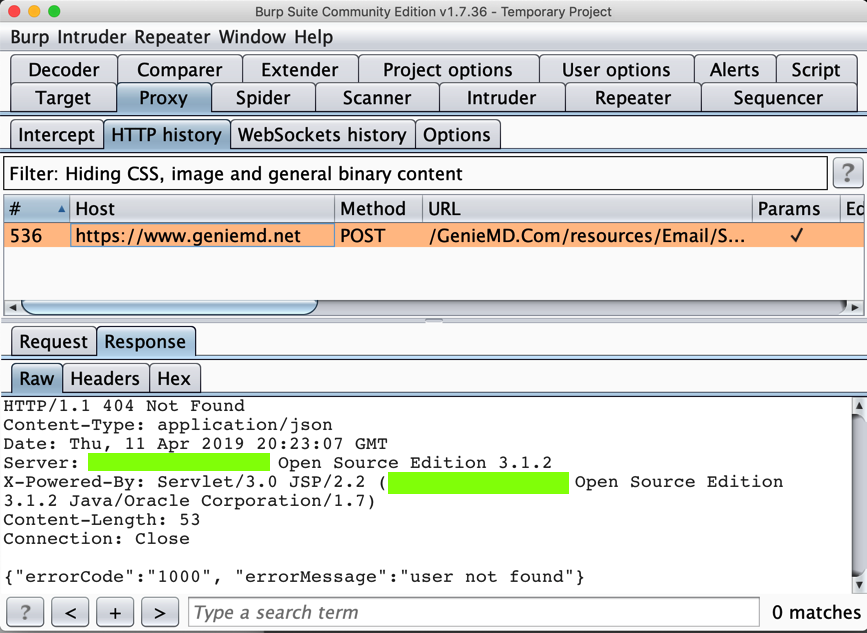
Execute a login request. The flag is the domain name of the server it sends a POST request to.
It asks for a registration code.
On your Kali machine, execute this command to unpack the app:
apktool d A31.2.apk