The same techniques work for Linux and Mac hashes, but thousands of times slower, because Windows uses especially weak hashes.
Here's a simple test case. A password of
password
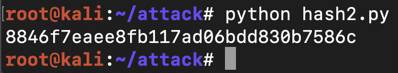
8846f7eaee8fb117ad06bdd830b7586c
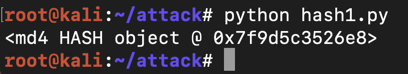
import hashlib
print hashlib.new('md4', 'password')
To see the normal result in hexadecimal, add the hexdigest() method like this:
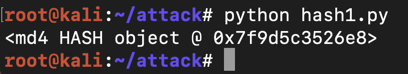
import hashlib
print hashlib.new('md4', 'password').hexdigest()
This looks more like a hexadecimal hash, but it's incorrect for Windows passwords. As shown above, the correct NT hash starts with 8846.
That's because the Windows algorithm uses Unicode, not ASCII, to encode the characters.
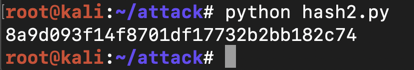
Modify your program to use Unicode, as shown below. (NOTE: the code for Unicode is "UTF-16LE" with the letters in lowercase, NOT "utf-161e".)
import hashlib
print hashlib.new('md4', 'password'.encode('utf-16le')).hexdigest()
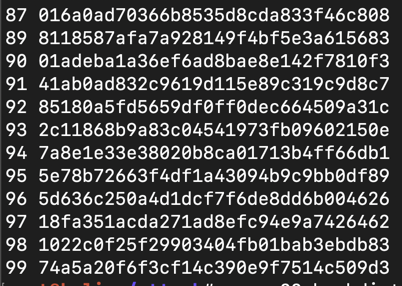
Find the hash containing 2343. That two-digit PIN is the flag.
CCSF-username-PINWhere "username" is the username in lowercase and PIN is a two-digit number.
For example, a user named "Sam" might have a password like this:
CCSF-sam-01Crack these passwords, which were collected from a Windows 7 machine with Cain.
Ming:"":"":AAD3B435B51404EEAAD3B435B51404EE:52C4859C0617E4A8FEC24BA890C5FC57
Mohammed:"":"":AAD3B435B51404EEAAD3B435B51404EE:39057EF3A9FE57D98E7A9BAB7CD2F4F9
sam:"":"":AAD3B435B51404EEAAD3B435B51404EE:19A641D2520B983ABB7C931CEFF933FA
The passwords are the flags, as shown below:
Somewhere in the Terms of Service, it strongly warns users not to re-use the same password as their Windows password.
In addition, it is now much more secure, because it uses MD5 instead of MD4, and not only that, it uses many rounds of MD5.
It doesn't use Unicode encoding.
Crack these hashes.
Ming: 7621eca98fe6a1885d4f5f56a0525915
Mohammed: b2173861e8787a326fb4476aa9585e1c
sam: 42e646b706acfab0cf8079351d176121
The passwords are the flags, as shown below:
So the new, super-enhanced system uses a much larger number of MD5 rounds, followed by an even larger number of SHA1 hash rounds. Of course, the total number of hashing rounds is less than 500, because management is sure that's enough.
And now each user has to click "I Agree" to a pop-up box requiring them not to re-use passwords, so only a complete idiot would do that.
Crack these hashes if you can! Send in the correct passwords to collect credit.
Ming: ce788ed5f855e51e6fd78f923b43a6407467c5f2
Mohammed: 582d99006950cddeb2df9f40b3f65ebc283dc378
sam: da660655f4d4714fe605e9063d1ded4b749c50a9
The passwords are the flags, as shown below:
Old hash generator site removed 4-7-19
Revised for WCIL 5-20-19
Explanation of PIN flag added 7-10-19